What is NIST-CSF?
The NIST cybersecurity framework is an effective tool for structuring and enhancing your cybersecurity program. It is a collection of standards and best practices meant to assist businesses in strengthening their cybersecurity posture. The framework offers instructions for responding to, preventing, and recovering from cyber disasters and a collection of standards and suggestions that help organizations recognize and detect cyberattacks more effectively.
This framework, created by the National Institute of Standards and Technology (NIST), tackles the shortage of cybersecurity standards and offers a consistent set of norms, regulations, and standards that businesses in all sectors can employ. Most people agree that the NIST Cybersecurity Framework (NIST CSF) is the best resource for developing cybersecurity policies and procedures. The NIST CSF is adaptable enough to work with any organization’s current security procedures, regardless of the sector. It offers a great place to start when implementing cybersecurity risk management and information security in almost any US private sector company.
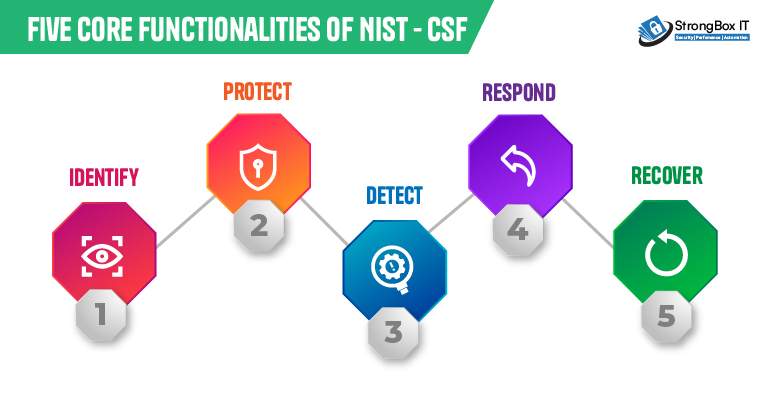
Five core functionalities of NIST – CSF
The core functionalities provide an extensive overview of the best practices for security protocols. Activities are carried out “concurrently and continuously to form an operational culture that addresses the dynamic cybersecurity risk” and not as phases in a procedure. Within an organization, categories and subcategories offer in depth action plans for particular departments or procedures.
1. Identify
The cybersecurity team must have an in-depth understanding of the company’s most valuable resources and assets to defend against cyberattacks. Asset management, business environment, governance, risk assessment, risk management strategy, and supply chain risk management are some categories included in the identified function. In this group, essential activities consist of:
- Determining software and hardware assets to lay the framework for an asset management program.
- Recognizing the business climate of the company and its place in the supply chain.
- Defining the governance program by identifying established cybersecurity rules and the legal and regulatory requirements for the organization’s cybersecurity capabilities.
- Assessing risk involves identifying organizational resource threats both within and externally, asset vulnerabilities and risk response actions.
- Establishing a risk tolerance and developing a risk management plan.
- Deciding on a supply chain risk management plan and including the goals, limitations, risk tolerances, and presumptions that underpin the risk management decisions.
2. Protect
The protection function is responsible for safeguarding important infrastructure and implementing security measures, including physical and technical security controls. These areas include maintenance, protective technology, data security, awareness and training, identity management and access control, and information protection processes and procedures.
- Installing local and remote access security measures for Identity Management and Access Control inside the company.
- Providing privileged user and role-based security awareness training to employees in order to empower them.
- Protecting information confidentiality, integrity, and availability by implementing data security measures in line with the organization’s risk management plan.
- Establish policies and procedures to manage and keep information systems and assets protected.
- Utilizing maintenance, incredibly remote maintenance, to safeguard organizational resources.
- Technology should be managed by corporate rules, processes, and agreements to guarantee system security and resilience.
3. Detect
The detect function sets precautions to notify a company about cyberattacks. Security, continuous tracking, deviations and occurrences, and detection procedures are examples of detection categories.
- Ensuring that occurrences and anomalies are found and their possible effects are comprehended.
- Implementing continuous monitoring tools to monitor cybersecurity incidents and confirm the efficacy of preventative measures, such as network and physical actions.
4. Respond
The response function categories guarantee that cybersecurity events, such as cyberattacks, are handled appropriately. Some specific categories are response planning, communications, analysis, mitigation, and enhancements.
- Ensuring that the response planning procedure is followed during and after an incident.
- Overseeing correspondence with external and internal stakeholders before and after an event.
- Assessing the occurrence to guarantee a successful reaction, assisting with recovery efforts such as forensic examination and incident impact assessment.
- Engaging in mitigation measures to stop an event from getting worse and to put an end to the incident.
- Implement improvements by considering the knowledge gained from recent and past detection and response operations.
5. Recover
Recovery operations carry out strategies for cyber resilience and guarantee uninterrupted business operations in the case of a cyberattack, security compromise, or other cybersecurity incident. Recovery planning enhancements and communication are recovery functions.
- Ensuring that to restore systems and assets impacted by cybersecurity incidents, the business follows recovery planning protocols and procedures.
- Implementing enhancements derived from analyses of current tactics and lessons discovered into practice.
- Coordination of communications between internal and external parties occurs both during and after the recovery from a cybersecurity event.
Why is the CSF important?
The CSF is crucial because it empowers organizations to manage cybersecurity risk proactively. Following its framework, you can identify weaknesses before they’re exploited, implement safeguards to protect your data and establish a plan to respond to and recover from attacks effectively. This reduces the risk of costly breaches and strengthens your overall cybersecurity posture, improving communication within your organization and potentially aiding compliance with regulations. Alignment with the NIST CSF can help organizations meet industry-specific or regulatory cybersecurity requirements.
StrongBox IT aligns with the NIST-CSF framework.
StrongBox IT has the experience in implementing security solutions that are aligned with the NIST CSF framework, that helps organizations to strengthen security posture, enhance compliance and improve threat detection. Here’s how:
- Security Assessments: We help you identify your vulnerabilities through comprehensive security assessments that align with the Identify function of the CSF.
- Security Solutions: We offer a range of security solutions, including firewalls, intrusion detection/prevention systems, and data encryption, to help you implement essential safeguards (Protect function).
StrongBox IT was created to be natively integrated and counteract cyberattacks before they even appear in the environment of an organization. Regardless of how or where apps and data exist or are utilized, organizations can prevent cyberattacks with complete visibility into traffic across the network, endpoints, and cloud. As a result, total cybersecurity risk can be decreased and the most significant continuing threats to vital business activities can be identified by critical infrastructure businesses.





