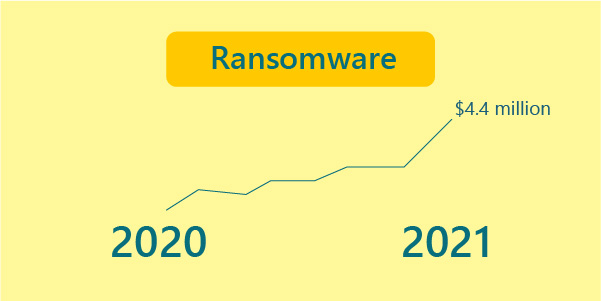
1. The Number of Ransomware Attacks Is Increasing
Ransomware has continued to grow and change in 2021, making it one of the most common dangers to any organization’s data security and ranks first in the cyber trends of 2021 Organizations are plagued by data theft and financial losses due to the costs of recovering from ransomware attacks. Ransomware assaults were more expensive than the usual data breach in 2020, costing an average of $4.4 million.
Many IT departments and enterprises use Virtual Private Networks (VPNs) to enable access to their corporate network., VPNs are insufficient. Phishing is the most popular entrance vector for ransomware. Enterprises should be aware that these assaults are rising. They must take appropriate precautions to protect themselves.
2.Platforms with zero trust proliferate.
The COVID-19 pandemic has hastened the transition to zero-trust platforms by forcing nearly the entire global workforce outside a specified network perimeter. The zero-trust strategy is based on four principles:
1. Any user can be hacked; no one should be trusted by default.
2. VPNs and firewalls can’t do it independently because they only protect the perimeter.
3. Rather than merely on the perimeter, identity and device authentication should occur throughout the network.
4. Micro-segmentation reduces hacker harm by erecting internal barriers.
Security functions are integrated into practically invisible tooling in good zero-trust platforms, so users have no choice but to work more securely. There is no such thing as a trusted source under the zero-trust approach. The model posits that “would-be attackers” exist both within and outside the network, which leads us to insider threats.
3.Threats from inside continue to lurk.
Insider risks are becoming a more significant worry as we negotiate a remote workforce. While it’s simpler to imagine that all cybersecurity dangers come from outside sources, businesses should be aware that threat actors could be hiding within their walls. It’s crucial to understand that insider dangers aren’t always present for workers. Former employees, contractors, or partners with access to an organization’s systems or sensitive information might potentially be suspects.

Companies must pay more attention to the prospect of insider threats and data theft by their staff in 2021 and beyond. While this is a tricky thing to swallow, the numbers don’t lie. Security breaches account for 15% to 25% of all data breaches.
4. Multi-factor authentication is a high-priority feature.
While STRONG passwords are still the gold standard for cybersecurity, more businesses are beginning to use multi-factor authentication (MFA) as an additional layer of protection against data breaches and cyberattacks. MFA entails using two or more distinct factors in permitting users to access sensitive data, requiring users to prove their identity with more than one device. A one-time passcode delivered to two or more devices is an example of MFA operating (like your cell phone and personal email).
Passwords are in high demand among cybercriminals. Cybercriminals can access your bank account, credit cards, and personal websites with an unprotected password. They can then sell your personal information or that of your employees, obtain access to your money, and jeopardize your company’s overall digital security.
5.Extensive Detection And Reaction (XDR)
By merging security information and event management (SIEM), security orchestration, automation, and response (SOAR), network traffic analysis (NTA), and endpoint detection and response (EDR), extended detection and response (XDR) centralizes security data (EDR). Increasing detection and response by gaining visibility across networks, clouds, and endpoints and correlating threat intelligence across security products.
According to Gartner, an XDR system must have a centralized incident response capability that can change the state of specific security products as part of the remediation process. The fundamental purpose of an XDR platform is to improve security operations efficiency and productivity by correlating threat intelligence and signals across numerous protection products.
6.Companies with a Specific Purpose to Acquire (SPACs)
For the first time, numerous cybersecurity firms seeking access to the public markets are foregoing an IPO in favour of merging with or being purchased by a publicly-traded shell company. Appgate, a secure access vendor, kicked things off in February when it announced a $1 billion merger with Newtown Lane Marketing, barely a year after splitting from data centre vendor Cyxtera.

QOMPLX, a risk analytics platform, bought two companies the next month and agreed to merge with Tailwind Acquisition Corp, a special purpose acquisition company (SPAC), for a $1.4 billion valuation. In March, network detection and response vendor IronNet Cybersecurity agreed to merge with LGL Systems Acquisition Corp, valuing the company at $1.2 billion.
7.Continued rise of AI
AI is an imminent part of cyber trends. Businesses will continue to develop AI and machine learning as part of their security architecture in 2022 as they become more sophisticated and capable. AI is increasingly being utilized to create automated security systems that substitute human intervention, allowing for far faster analysis of enormous amounts of risk data. This is advantageous for large firms dealing with vast amounts of data and small and mid-sized businesses with under-resourced security teams.

While AI presents a significant opportunity for businesses to improve their threat detection, innovation, and more meaningful applications have positive and negative implications. Criminal networks are using AI to automate their attacks, and they’re using strategies like data poisoning and model theft to do so.
8. Attacks on cloud services are becoming more common.
With the broad acceptance of remote work resulting from COVID-19, the demand for cloud-based services and infrastructure has skyrocketed. As more firms implement cloud-hosted procedures in 2022 and beyond, this tendency will only continue to expand.
While cloud services have numerous advantages like scalability, efficiency, and cost savings, they remain a prime target for cybercriminals. As a result, organizations will need to assess the security implications of cloud computing and identify any weaknesses in their current infrastructure. Misconfigured cloud settings, for example, were a prominent source of data breaches in 2021, costing an average of $4.41 million. Furthermore, moving to the cloud increased the cost of the violation by $267,469.
9.Data Privacy
As a discipline, data privacy is concerned with protecting personal information.
Concerns regarding data privacy, management, and security have increased due to a growing number of high-profile cyber intrusions that have exposed millions of personally identifiable information (PII) records. As a result, data privacy will no longer be a single component of a security program in 2022 but will become its program. In addition, organizations will be expected to focus on their data privacy initiatives moving forward as regulatory compliance requirements have continued to rise and will continue to grow in 2022.
10.The need for real-time data visibility is critical.
While many executives manage cybersecurity risks for specific areas of their businesses, their efforts are hampered by a lack of a holistic view of the organization’s technology ecosystem.
For example, many executives don’t have a thorough inventory of their IT assets or a list of all third-party suppliers and cloud applications that their company uses. Because risk assessment programs are generally dependent on stocks that lack a complete and accurate image of the threat landscape, resulting in weakened risk assessment programs.





