Data security in cloud computing refers to the set of technical solutions, policies, and procedures you use to safeguard cloud-based apps and systems, as well as the data and user access they include.

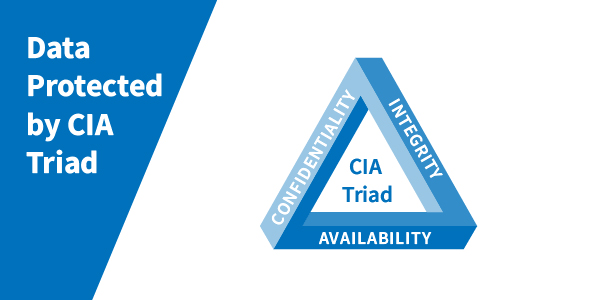
Data confidentiality, integrity, and availability (known as the CIA trinity) are key concepts of information security and data governance, and they apply to the cloud as well:
Confidentiality: It refers to the safeguarding of data from unauthorised access and disclosure.
Integrity: Protect the data from unauthorised changes so that it can be trusted.
Availability: Ensuring that data is completely accessible and available when it is required.
These principles are true regardless of:
- Which cloud model you use public, private, hybrid, or community clouds is a personal decision.
- Which cloud computing category do you prefer: software-as-a-service (SaaS), platform-as-a-service (PaaS), infrastructure-as-a-service (IaaS), or function-as-a-service (FaaS)
- From the creation, implementation, or migration of applications and systems through the administration of the cloud environment, data security must be considered at all stages of cloud computing and the data lifecycle.
Threats to data security from cloud computing
While the same cybersecurity dangers that affect on-premises equipment also affect cloud computing, the cloud introduces new data security risks.
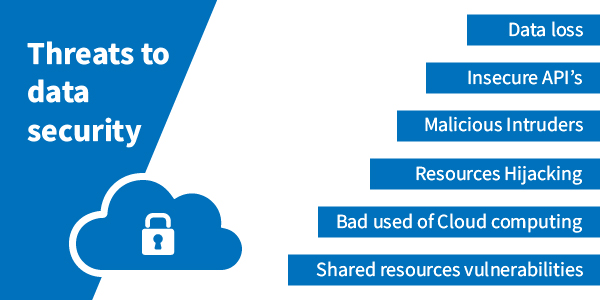
Insecure application programming interfaces (APIs)
Many cloud services and applications rely on APIs for features like authentication and access, yet these interfaces frequently include security flaws like misconfigurations, allowing for compromises.
Account hijack or takeover
Many users use weak passwords or reuse hacked passwords, making it easy for cybercriminals to gain access to cloud accounts.
Insider threats
While not unique to the cloud, the lack of visibility into the cloud ecosystem increases the potential of insider threats, whether insiders are gaining unauthorised access to data with malicious intent or sharing or storing sensitive data mistakenly.
Data security safeguards in cloud computing
Identity governance is the foundation of cloud data security. You require a unified, comprehensive view of data access across on-premises and cloud platforms and workloads.
Identity governance delivers the following benefits:
- Ineffective access control stems from a lack of visibility, which increases both your risks and expenditures.
- Federated access by leveraging your Active Directory or other systems of record, reduces the need for manual management of distinct identities.
- Monitoring to see if cloud data access is approved and appropriate.
- Automating processes to relieve the burden on your IT team, as well as assessing your security tools on a regular basis. It ensures continuous risk mitigation as your environment grows, which are examples of governance best practices.
Here are some data security protections for cloud computing that we recommend:
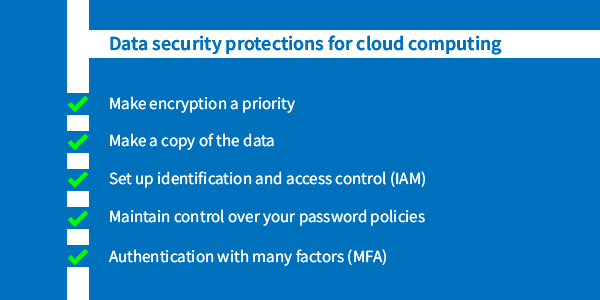
Make encryption a priority
Ensure that sensitive and vital data, such as personally identifiable information (PII) and intellectual property, is encrypted in transit and at rest.
Because not all providers provide encryption, you should consider using a third-party encryption solution for extra security.
Make a copy of the data
While suppliers may have their own backup protocols, it’s still a good idea to backup your cloud data locally.
When backing up data, follow the 3-2-1 rule:
- Maintain at least three copies
- Store them on at least two separate media
- One offshore backup should at least be retained (in the case of the cloud, the offsite backup could be the one executed by the vendor).
Set up identification and access control (IAM)
The proper individuals have appropriate access to data thanks to your IAM technology and policies, and this framework must include your cloud environment.
Access management and privileged access management are two IAM components in addition to identity governance.
Maintain control over your password policies
Poor password hygiene commonly causes data leaks and other security mishaps
Make it easy for your staff and other end-users to utilise secure password habits by implementing password management systems.
Authentication with many factors (MFA)
Multi-factor authentication uses strong password policies. It is one of the effective techniques which prevents the password from being compromised.
It adds another barrier for threat actors to overcome when attempting to obtain access to your cloud accounts.





