OWASP
The Open Web Application Security Project (OWASP) is an online nonprofit initiative that derives a set of rules or protocols, articles, methodologies in the field of cyber security. It works on an open-source model where various users contribute tools, forums, and projects. OWASP is the repository of web application security modules.
ModSecurity
ModSecurity is an open-source, cross-platform, Web Application firewall designed primarily for Apache HTTP servers. It provides an event-based programming language that offers protection from a wide range of attacks and offers protection to web applications.
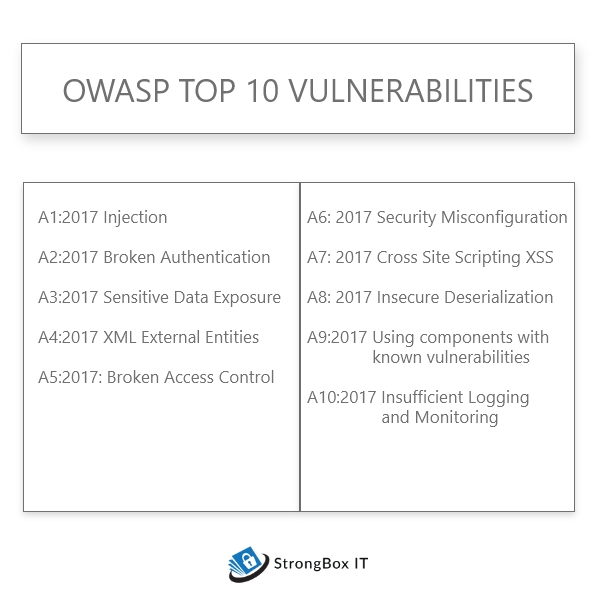
What are the OWASP top 10 vulnerabilities or threats?
Based on the level of damages the vulnerabilities have caused, OWASP has derived a list of top 10 threats. These threats are categorized from A1 to A10, A1 being the most severe and A10 being the least.
OWASP’s top 10 vulnerabilities are as follows
- A1:2017 Injection
- A2:2017 Broken Authentication
- A3:2017 Sensitive Data Exposure
- A4:2017 XML External Entities
- A5:2017: Broken Access Control
- A6:2017 Security Misconfiguration
- A7:2017 Cross Site Scripting XSS
- A8:2017 Insecure Deserialization
- A9:2017 Using components with known vulnerabilities
- A10:2017 Insufficient Logging and Monitoring
A1: 2017 Injection: SQL injection attacks the database when a malefactor executes a discreet code on the host operating system through a vulnerable application. It prevents sending data to the interpreter of the query, which could lead to data loss, data corruption, and loss of credibility. It is listed as the most dangerous threat in OWASP top 10 vulnerabilities
Common types of injection are,
- SQL
- NoSQL
- Object Relational Mapping(ORM)
- Expression Language(EL)
- OS command
A2: 2017 Broken Authentication: Broken authentication is theft of user credentials, session tokens, keys, etc.. to gain unauthorized privilege. Attackers try broken authentication manually and attack them by using password lists and automated tools. Based on the domain, this may lead to money laundering, identity theft, social security fraud, and sensitive information disclosure. It is listed as the second most dangerous threat in OWASP top 10 vulnerabilities
A3: 2017 Sensitive Data Exposure: Sensitive data exposure is the exposure of sensitive data carelessly thereby leading to a breach in the entire system. The data being obtained is being sold or modified to conduct fraudulent activities. It is ranked third in OWASP top 10 vulnerabilities
A4: 2017 XML External Entities: XML External Entity injection is the type of threat that allows an attacker to access an application’s XML data processing files. It takes place on poorly configured XML processors that allow external entity references within XML documents. It may cause subjugation of important assets using the URI handler, internal file shares, internal port scanning, remote code execution, and denial of service attacks. It is ranked fourth in OWASP top 10 vulnerabilities
A5: 2017 Broken Access Control: The failure of the system to validate the user even after the user authentication is called Broken Access Control. This allows the user to bypass the basic access controls without proper validation. This leads to admin-level data exposure which in turn may lead to several other complications. It obtains fifth place in OWASP’s top 10 vulnerabilities.
A6: 2017 Security Misconfiguration: Misconfiguration occurs whenever the system fails to meet the security framework standards. It may occur at the application server-side, web server-side, application stack level, or even at the network side. Non-identification of these flaws may sabotage and compromise the entire system. It is listed as the sixth most serious threat OWASP top 10 vulnerabilities.
A7: 2017 Cross-Site Scripting XSS: XSS flaw occurs whenever the attacker makes use of DOM and API to retrieve data or send commands to the application. Cross-site scripting may widen the surface of the attack for the hacker by allowing him to hack user credentials, spread worms, and control browsers remotely. This can lead to credential theft and help in delivering malware to the victims.
A8: 2017 Insecure Deserialization: It is a vulnerability that occurs when malicious data is used to disturb the logic of an application. It induces denial of service attacks or misapplies the logic of an application upon deserialization.
Improper handling of this flaw may entertain remote code execution attacks.
A9:2017 Using components with known vulnerabilities: Usage of third-party software components in the development process may lead to this type of attack. Known components like third-party application frameworks, libraries, technologies that may have exposure to major vulnerabilities. These kinds of threats are often difficult to exploit and cause serious data breaches.
A10:2017 Insufficient Logging and Monitoring: Lack of logging and monitoring the threats to the application from time to time causes these types of attacks. It may lead to compromising the entire system and an untraceable attack.





